Selfhosted
A place to share alternatives to popular online services that can be self-hosted without giving up privacy or locking you into a service you don't control.
Rules:
-
Be civil: we're here to support and learn from one another. Insults won't be tolerated. Flame wars are frowned upon.
-
No spam posting.
-
Posts have to be centered around self-hosting. There are other communities for discussing hardware or home computing. If it's not obvious why your post topic revolves around selfhosting, please include details to make it clear.
-
Don't duplicate the full text of your blog or github here. Just post the link for folks to click.
-
Submission headline should match the article title (don’t cherry-pick information from the title to fit your agenda).
-
No trolling.
Resources:
- selfh.st Newsletter and index of selfhosted software and apps
- awesome-selfhosted software
- awesome-sysadmin resources
- Self-Hosted Podcast from Jupiter Broadcasting
Any issues on the community? Report it using the report flag.
Questions? DM the mods!
view the rest of the comments
You already have a lot of good answers ... but I got one more to add.
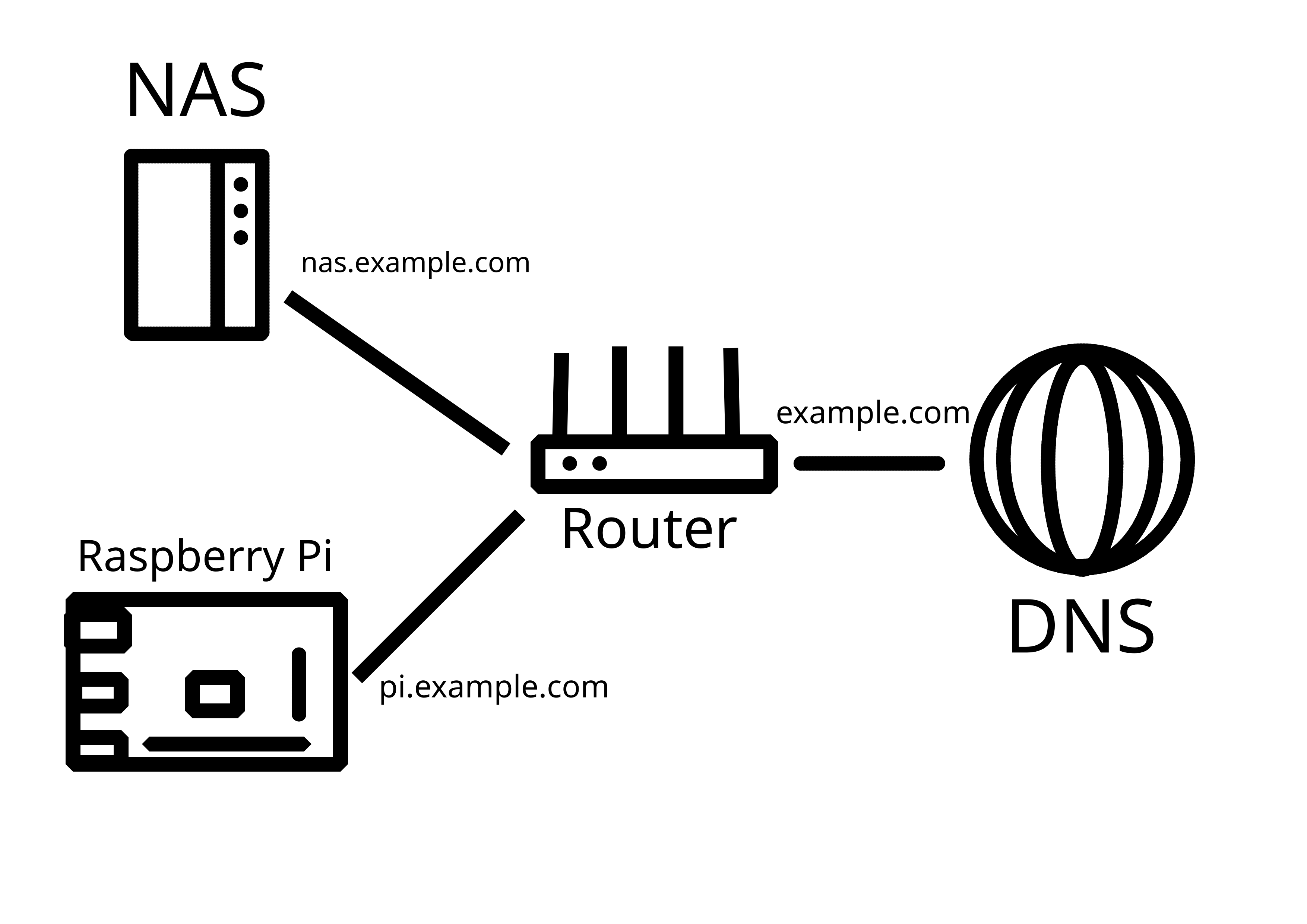
I have a very similar setup on my homelab and I'm using a Cloudflare tunnel.
It's a free service and it's really good because it allows you to expose web services and specific ports for remote access over dynamic IPs without having to expose your own router.
https://developers.cloudflare.com/cloudflare-one/connections/connect-networks/
Thanks! I got that advice as well, but I would like to keep it self-hosted - I consider using Pangolin on a VPS for that purpose going forward: https://github.com/fosrl/pangolin
Also, beware of the new attack on Cloudflare Tunnel: https://www.csoonline.com/article/4009636/phishing-campaign-abuses-cloudflare-tunnels-to-sneak-malware-past-firewalls.html
This attack targets end users, not Cloudflare tunnel operators (i.e. self-hosters). It abuses Cloudflare Tunnels as a delivery mechanism for malware payloads, not as a method to compromise or attack people who are self-hosting their own services through Cloudflare Tunnels.
Thanks for clarification!