Selfhosted
A place to share alternatives to popular online services that can be self-hosted without giving up privacy or locking you into a service you don't control.
Rules:
-
Be civil: we're here to support and learn from one another. Insults won't be tolerated. Flame wars are frowned upon.
-
No spam posting.
-
Posts have to be centered around self-hosting. There are other communities for discussing hardware or home computing. If it's not obvious why your post topic revolves around selfhosting, please include details to make it clear.
-
Don't duplicate the full text of your blog or github here. Just post the link for folks to click.
-
Submission headline should match the article title (don’t cherry-pick information from the title to fit your agenda).
-
No trolling.
Resources:
- selfh.st Newsletter and index of selfhosted software and apps
- awesome-selfhosted software
- awesome-sysadmin resources
- Self-Hosted Podcast from Jupiter Broadcasting
Any issues on the community? Report it using the report flag.
Questions? DM the mods!
view the rest of the comments
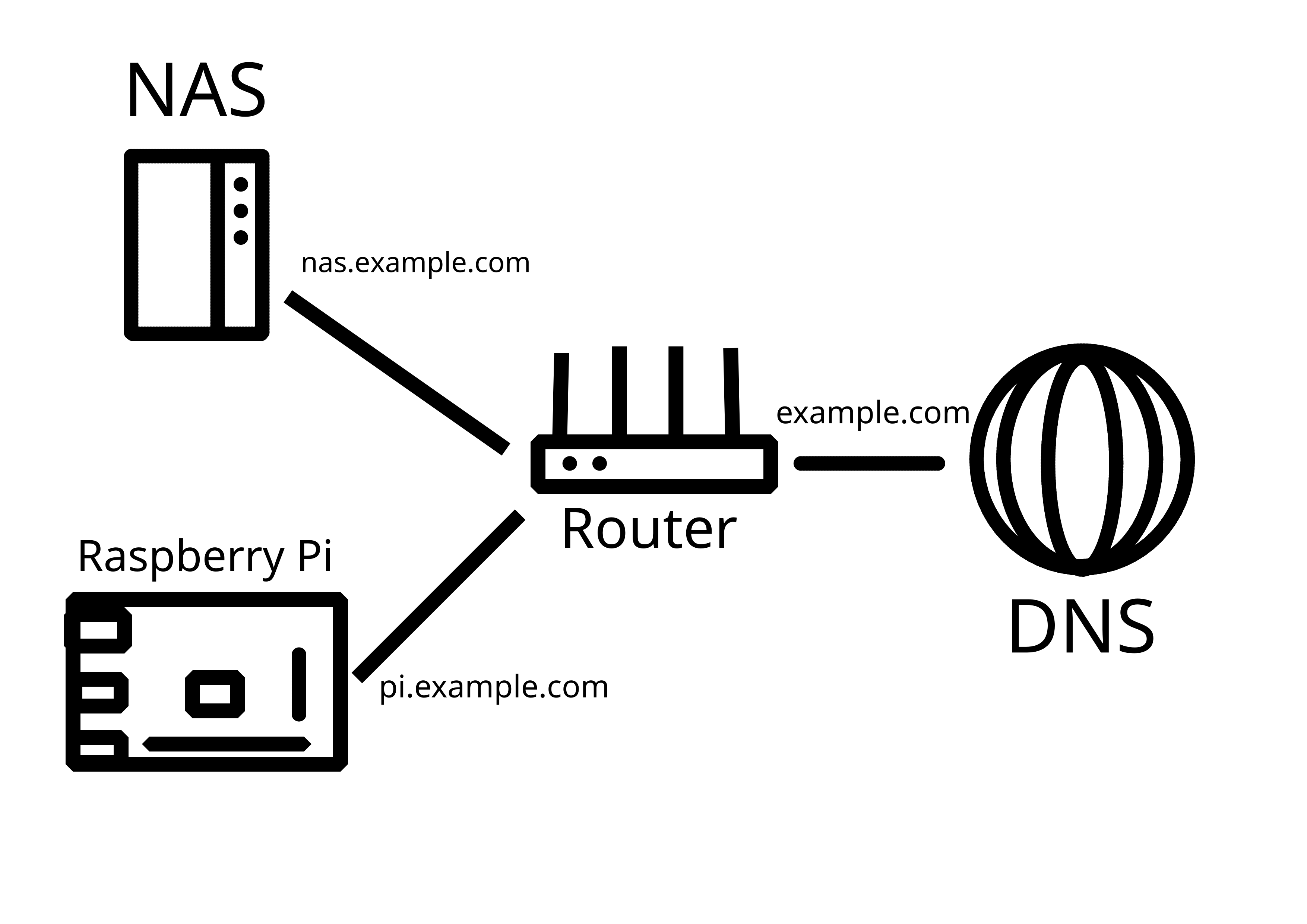
I really feel like people who are beginners shouldnt play with exposing their services. When you set up Caddy or some other reverse proxy and actually monitor it with something like fail2ban you can see that the crawlers etc are pretty fast to find your services. If any user has a very poor password (or is reusing a leaked one) then someone has pretty open access to their stuff and you wont even notice unless you’re logging stuff.
Of course you can set up 2FA etc but that’s pretty involved compared to a simple wg tunnel that lives on your router.
For now I'm only toying around, experimenting a little - and then closing ports and turning my Pi off. I do have my NAS constantly exposed, but it is solidly hardened (firewall, no SSH, IP bans for unauthorized actions, etc. etc.), fully updated, hosts no sensitive data, and all that is important is backed up on an offline drive.
My mantra is "plan to be hacked". Whether this is a good backup strategy, a read-only VM, good monitoring or serious firewall rules.